OpenAEV 2.1: Security Control Validation, Broadened Integrations, New Widgets, and more…

OpenAEV – the leading open-source, threat-informed exposure validation platform – is receiving some new and enhanced capabilities driven by its rapidly growing community.
In this latest release, OpenAEV introduces new Security Control Validation management feature, highly request integrations, key UI/UX updates, and performance improvements for running large‑scale scenarios .
This blog highlights some of the major updates that you can find. For more information, see you on the Filigran OpenAEV community !
TL;DR
- Domain‑Based Security Control Validation brings clear, visual insights into exposure risks across eight standardized security domains.
- New integrations with Palo Alto Cortex XDR, SentinelOne, and Shodan widen OpenAEV’s ecosystem and improve automation.
- New Security Coverage widget and UI improvements make dashboards more actionable and scenario creation faster.
- OpenCTI Security Coverage enhancements improve scenario execution accuracy with new validity periods, execution intervals, and automatic asset selection.
- Significant scalability improvements now allow attack emulation across thousands of endpoints without performance degradation
Domain-Based Security Control Validation
The OpenAEV 2.1 release introduces a new intuitive system for SOC teams to gain immediate visibility into their attack surface vulnerabilities: domain-based Security Control Validation.
This domain-driven approach to exposure validation provides a practical and visual system to highlight critical exposure risks and quickly drill down into specific weak points that could compromise an entire domain.
This actionable snapshot was built to enable both SOC managers and practitioners alike to immediately see where attention is needed, and support quick decision making from more effective prioritization.
As always with Filigran, this system is based on widely adopted, industry-standard practices such as MITRE ATT&CK heatmaps, SOC dashboards, and ISO/IEC 27001.
What is a Security Domain?
A Security Domain represents a major area of exposure that must be tested, measured, and validated independently. Together, these domains provide an accurate representation of your attack surface.
OpenAEV now structures security control validation across eight standardized domains:
- Endpoint: Protection and detection on user devices and servers
- Network: Lateral movement visibility and network-based attack detection
- Web Application: Security of exposed applications and APIs
- E-mail Infiltration: Phishing, malware, and social engineering defenses
- Data Exfiltration: Detection and prevention of outbound data leakage
- URL Filtering: Control of malicious or risky web destinations
- Cloud: Security posture and detection across cloud workloads and services
- Table-Top: Scenario-based exercises modeling attacker behavior without executing technical actions
Security Coverage dashboard widget
You can now add and customize a new Security Coverage widget to any of your dashboards, providing a instant, snapshot visual indicator of your attack surface vulnerability across your 8 security domains.
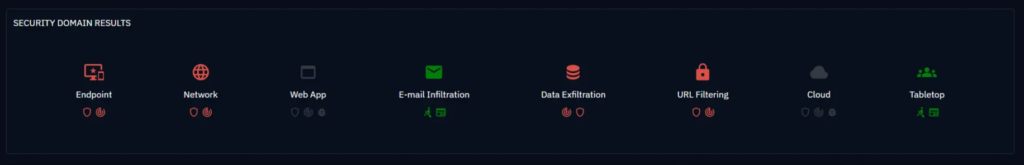
The indicator is color-coded to represent a strong🟢, partial🟠, week🔴, or missing⚪ coverage across, following the concept of “the worst color wins”. That is, if one sub-domain shows as critical, this will determine the main domain’s status even if the other sub-domains are strong.
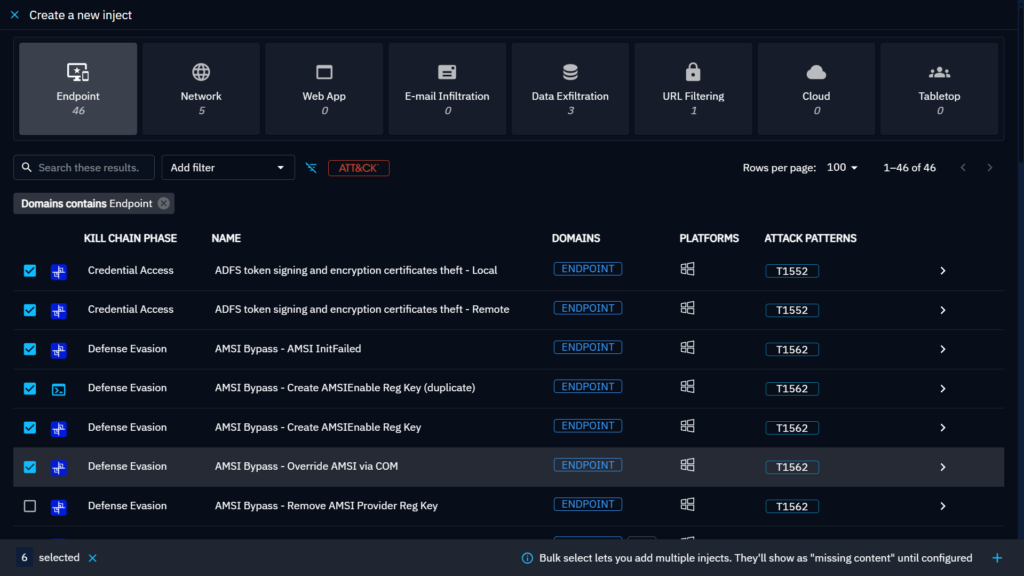
Domain assignment & filtering to simplify scenario creation
You can easily configure your Security Domains by assigning your payloads and contracts to one or more domain. Scenario creation now includes visual domain filters and bulk selection for injects to simplify and accelerate scenario configuration. This assignment will then automatically feed into your Security Domain metrics and widgets.
Who will benefit from this approach?
- SOC Managers: you can now identify and drill down into weak detection areas by domain
- SOC Analysts: You can create more insightful scenarios and select atomic tests faster
- Blue Team Leads: You can now prioritize remediations by specific domain risks
- CISOs: You can more accurately track and report on readiness KPIs by attack surface
New Integrations
One of OpenAEV’s key objective is to remain one of the most open and flexible Exposure Management products on the market. To do so, we are consistently broadening our integrations catalog to ensure compatibility with all kinds of security stacks and the ability to retrieve security intelligence from a wide range of external sources.
In the release, we are glad to introduce new and highly-request integrations with Palo Alto, Sentinel One, and the Shodan Search Engine.
Sentinel One Executor
You can now deploy the new Sentinel One executor directly from your OpenAEV integrations catalog. This will broaden the agentless capabilities of the product by enabling Remote Script Orchestration on SentinelOne to execute scenarios on endpoints through OpenAEV.
Palo Alto Cortex XDR – Collector and Executor
Collectors are a key aspect of OpenAEV, enabling the automatic collection of alerts, logs and traces related to attacks, incidents or crisis by leveraging third-party SIEM, XDR, EDR, and NDR. With Palo Alto Cortex being such a widely used XDR, we are proud to now include it as part of OpenAEV’s catalog.
Alongside this collector, we are also releasing the Palo Alto Cortex XDR Executor, enabling users to execute scenarios also through their Palo Alto instance.
Shodan Injector
For many cybersecurity practitioners, the Shodan Search Engine is a key reference to gather public intelligence about which of their assets are exposed on the internet: if you can see something on Shodan, everyone can see it. But gathering and correlating this information to make it actionable is very time consuming.
The Shodan Injector enables users to automatically import exposures detected on Shodan and create assets based on the results, directly from OpenAEV. Users can then create appropriate findings to make this intelligence actionable as a part of their overall exposure management process.
The Shodan Injector will include the following searches:
- Domain / hostname discovery
- Host Enumeration
- CVE-specific watchlist
- Critical ports (RDP/SSH/SMB) / exposed admin interfaces
- Cloud Providers
OpenAEV Integrations Catalog
OpenAEV 2.1 greatly facilitates the management and deployment of connectors.
You can now browse through a full catalogue of pre-configured injectors, collectors, and executors to deploy directly from OpenAEV. This simplification, which replicates the OpenCTI Integration Manager, enables users to install and modify their integrations from the platform, removing the headache of having to perform manual configurations.
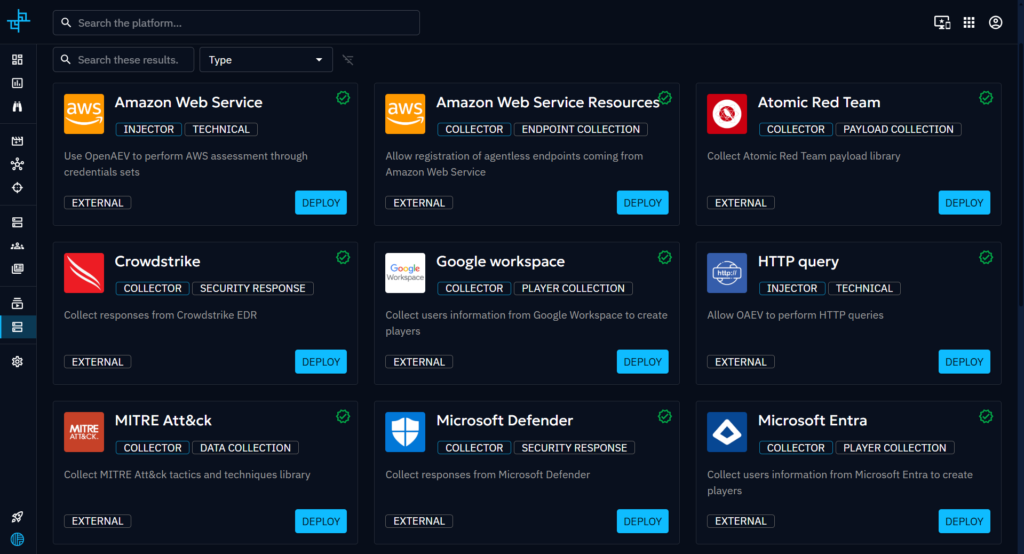
This feature is compatible with current RBAC preferences, so only users with the required permissions can deploy or modify your connectors.
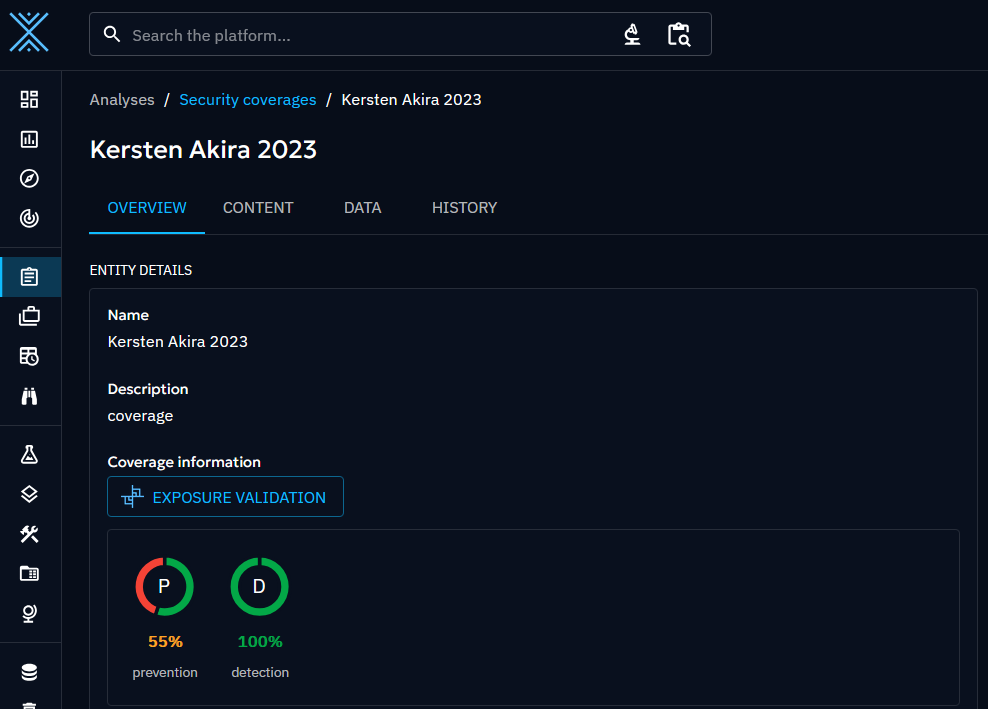
Security coverage improvements in OpenCTI
Filigran’s XTM platform is able to drive accurate CTI-driven exposure validation management by combining the capabilities of both OpenCTI and OpenAEV. One example of this is through the Security Coverage feature, which enables users to evaluate a threat directly from OpenCTI, by triggering OpenAEV scenarios.
OpenAEV 2.1 continues to improve on this feature by enhancing how Security Coverage scenarios are defined, executed, and aligned with OpenCTI platform configurations, making scenario analysis more accurate and easier to manage. Security Coverage now includes:
- Scenario Validity Period: A start and end date for the scenario
- Execution Interval: How often the scenario runs
- Immediate Launch: Execution of scenario upon creation
- Automatic Asset Assignment: Ensure the correct environments are targetted and respect of platform affinity (Windows/Linux/MacOS)
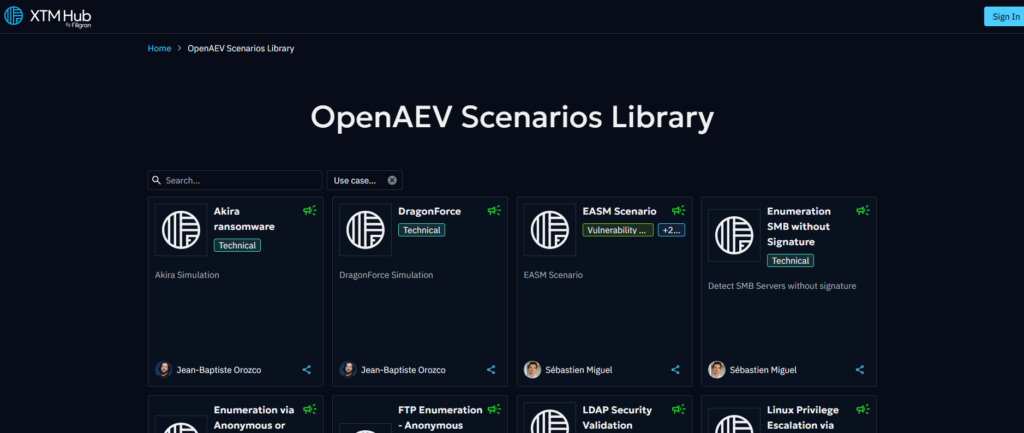
New content in the Scenario Library
Have you been to the Scenario Library recently? You’ll be surprised to find new pre-configured scenarios that you can import in a single click from the XTM Hub!
Notably, around the 2.1 release, you’ll fin the following:
- Possible dllhost.exe Spawning
- Linux Privilege Escalation via Find Command
- Windows Local Administrator Credential Stuffing
- Suspicious PowerShell Download Cradle Activity
- SQLI Enumeration
- Suspicious File Access Patterns
We have big plans to increase OpenAEV’s Scenario Library to accelerate scenario deployment and make our users’ lives easier – so keep an eye out!
You can access the full list on the XTM Hub right here.
Enhanced Scalability: Emulate attacks on thousands of endpoints
Last but not least, we are happy to introduce significant performance enhancements to improve the OpenAEV’s scalability. This update is made to cater for large organizations looking to manage scenarios that emulates attacks across a large amount of endpoints without impacting performance.
Conclusion
OpenAEV 2.1 strengthens its position as a leading open-source exposure validation platform by combining clearer security domain visibility, stronger integration capabilities, and enterprise‑level performance. Whether for SOC managers, analysts, or CISOs, this release offers more automation, better prioritization, and deeper intelligence to accelerate threat-informed defense.
Enjoy and feel free to ask any questions about it on our Slack community channel !
Interested in trying out OpenAEV? Just reach out and book a personalized demo
Read more
Explore related topics and insights






