CTEM But Without the Hype: Turning Intel and Validation into Outcomes
Cybersecurity teams have never had more tools, more threat feeds, or more vulnerability data. Yet the hardest questions remain unanswered: Which exposures matter to us? Are they exploitable here? Are we exposed to this campaign? Do our controls actually work? The gap isn’t tooling in cybersecurity – it’s turning raw information into relevant, actionable intelligence and proving we’re responding to what adversaries are doing, not just what scanners find. We’re rich in noise, poor in signal.
This is what a recent framework, Continuous Threat Exposure Management (CTEM) is trying to tackle. Is the concept that new though? What makes it more achievable now? Gartner says 60% of organizations are already pursuing or considering a CTEM program. Are you one of them, or why not? Read on, if you would like to:
- Understand what CTEM is
- Drivers for CTEM
- Why you shouldn’t believe the hype and ask challenging questions to vendors
- Finally, a quick look at our capabilities related to CTEM and how we can help
What is CTEM?
CTEM is a Gartner originated term and described as systematic, ongoing program for identifying, prioritizing, and reducing an organization’s exploitable exposure across its entire attack surface. It a continuous loop of proactive security with five key stages:
- Scoping: Agree on what matters. Assets, business processes, likely adversaries, ATT&CK focus. The scoping stage focuses security teams on the business aspects most important to senior management and to the reputation and operational viability of the organization.
- Discovery: Build the picture of what is exposed. Assets, controls, attack surface, exposures, and pathways.
- Prioritization: Decide what to fix or test first based on adversary relevance and probable impact.
- Validation: Which exposures are actually exploitable. Prove reality with safe, controlled attack emulations; measure control efficacy.
- Mobilization: Turn findings into durable change by remediation and process changes.

What’s different, why now?
At the core of CTEM is continuous, adaptive security, which is not a new concept of course. Gartner is famous for churning out new acronyms and some of you might remember, Continuous Adaptive Risk and Trust Assessment (CARTA) model, which was based on continuous adaptive evaluation of risk and trust across users, devices, and applications, moving away from static, one‑off decisions. Extend this to risk-based vulnerability/exposure/attack surface management, threat-led prioritization and continuous validation, and we move to CTEM. Its not a single tool but an internal framework to implement continuous, adaptive security, in which AI and automation play key roles.
Broadening vulnerability management towards exposure management
Traditional vulnerability management follows a predictable pattern: scan comprehensively, prioritize by CVSS score, generate remediation backlogs, and task engineering teams accordingly. Comprehensiveness takes over relevance, generating extensive backlogs burying critical exposures beneath thousands of low-relevance findings. More than 40,000 CVEs were published in 2024, creating backlogs too large to act on intelligently. The whole approach lacks validation mechanisms; to know which vulnerabilities are truly exploitable or if existing controls would detect exploitation attempts. This creates a false sense of security based on patch counts rather than demonstrated resilience against realistic attack scenarios.
So, what is changing now? As threat actors increasingly compress exploitation timelines, time is of essence to close the gap between identifying a threat and actioning on it. Vulnerability management’s effectiveness can be greatly improved when layered with business context such as asset criticality, data sensitivity, and the consequences of compromise, to be able to do a meaningful risk evaluation. And, this is exactly what are seeing as a positive change in 2025, modern platforms being accessible to organizations that are redefining how exposure is measured, modeled, and remediated by focusing on what attackers can truly reach and exploit. Mapping internal asset landscape with visibility into how these assets appear to external threat actors makes us understand exposure much better. Exposure management tools integrate threat intelligence, asset discovery, validation mechanisms and orchestrated response capabilities into a unified operational framework. The objective is to systematically reduce exploitable pathways before adversaries can weaponize them, transforming security operations from incident response to risk prevention.
Strategic role of threat intelligence for prioritization and contextualization
94% of vulnerabilities are never exploited. Gartner’s research confirms it but that means you’re wasting resources if you treat every CVE equally. Threat Intelligence can help you zero in on the 6% that matter for your organization by connecting vulnerabilities to adversary tactics, techniques, and procedures (TTPs) observed in active campaigns. Starting point should be defining your Priority Intelligence Requirements (PIRs): the questions that matter most to your organization. Layer it with threat intelligence that’s strategically relevant, filtered by your sector, region, adversaries, and the technologies you actually use. This prioritized threat intelligence tells you which flaws are being weaponized, against which targets, and under what conditions, so you can focus remediation on what’s exploitable in your environment, not what’s theoretically possible. This threat intelligence can also be seamlessly integrated into existing security stacks, making it actionable across the organization, from the SOC to the C-suite.
Evolution of continuous security validation
Security validation is undergoing a significant transformation as organizations adopt more strategic and proactive methods to assess their true security posture. Given the proliferation of heterogeneous tools within modern security stacks, it is essential to systematically validate the effectiveness and coverage of these controls. This shift is enabled by two critical capabilities that security leaders have long sought and that are now converging: exposure management as we discussed previously and continuous security validation, which offers ongoing assurance in defensive performance. Together, these capabilities allow CISOs to move beyond static assessments (like breach and attack simulations and tool-centric reporting (like pen testing) toward evidence-based, outcome-focused security governance. Adversarial Exposure Validation (AEV) is emerging as a crucial component of CTEM. AEV tools enable ‘continuous’ security assessment through simulations to create a context-aware validation and remediation ecosystem that finally answers the question: what can actually hurt us and how do we stop it?
Read more in our blog, BAS to AEV and a Move Towards Unified Exposure Management
Ability to assess security posture holistically – tools, processes and people
Validating security effectiveness cannot stop at tools alone; it must encompass technology, processes, and people as an integrated system. A perfectly tuned EDR, SIEM, or WAF offers limited protection if your incident workflows are unclear, playbooks are outdated, or escalation paths break under pressure. Similarly, well-documented procedures are ineffective if your security team, executives or your communication team have not rehearsed them under realistic conditions. True assurance comes from validating end-to-end: confirming that controls detect and prevent relevant threats, processes reliably move alerts to decisions and actions, and teams can execute their roles with speed and consistency when it matters. By testing tools, processes, and people together through continuous, threat-led exercises, organizations replace assumptions with evidence and transform security from a collection of products into a cohesive, resilient capability.
Read more in our article, Beyond Tools: Why Testing Human Readiness is the Hidden Superpower of Modern Security Validation
Avoid the hype – look for demonstrable real capabilities
CTEM has quickly become a buzzword, with many vendors showcasing polished frameworks and reference diagrams while delivering little beyond rebranded scanning and dashboards. Very few programs today go beyond visibility and run a continuous, threat-led loop. Do not be misled by the hype: CTEM is not a capability that vendors can simply ‘deliver’, but its an internal operating model that organizations must design and own. It is a strategic framework for aligning cyber risk with business risk and objectives, deciding which exposures to prioritize, and defining how exposure management is governed and executed. Tools play an important role, but only as enablers of this strategy – not as its substitute or starting point.
When evaluating CTEM claims, customers should press for hard evidence and specifics:
- How do you prioritize threats/exposure that really matter to you?
- Which adversary techniques can you actually model and validate in my environment?
- How do you prove exploitability and control efficacy, not just list vulnerabilities?
- What concrete workflows, integrations, and metrics support continuous operation rather than one-off reports?
Filigran’s Role in CTEM: Context In, Evidence Out
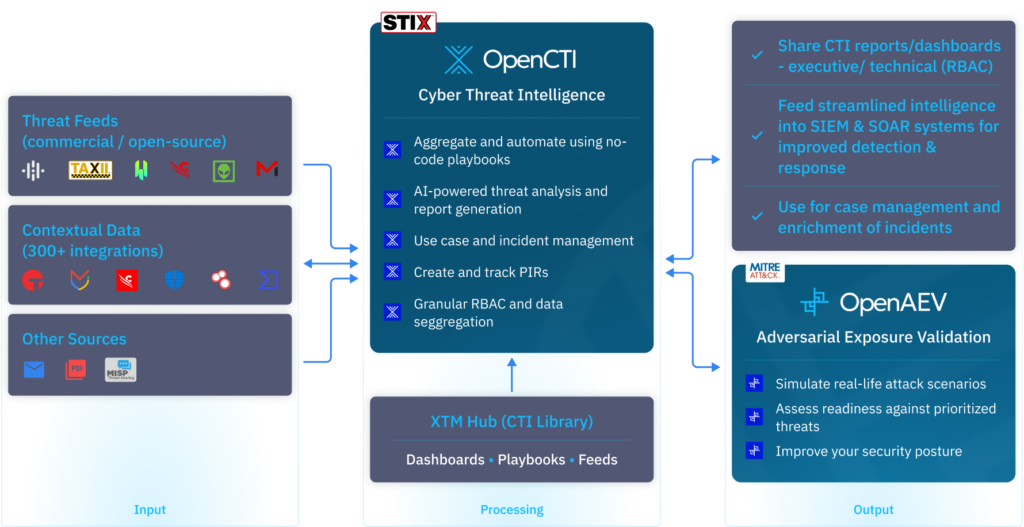
Filigran’s OpenCTI and OpenAEV can support a CTEM program by enabling key parts of the operating model rather than trying to replace it. As a Threat Intelligence Platform (TIP), OpenCTI provides the structured threat context needed for scoping, discovery, and prioritization (using PIRs). With industry standard frameworks like STIX 2.1, MITRE ATT&CK, you can model adversaries, techniques, vulnerabilities, assets, and relationships in a knowledge graph and with clear visualizations, so you can see which exposures map to real campaigns and likely routes to impact in your environment. This actionable threat intelligence can greatly improve threat detection and response.
OpenAEV complements this even further by operationalizing the validation and mobilization stages: it allows you to emulate relevant attack techniques safely, measure whether your controls detect and block them, and feed results back into your detections and remediation workflows. You can execute technical exercises like pen testing and tabletop exercises both from within OpenAEV. Moreover, tight integration between the two products allows a continuous loop of threat assessment and exposure validation, while keeping strategy, risk appetite, and prioritization decisions firmly in the hands of your organization.
Now, instead of chasing CVE counts, you prove outcomes: “We validated this route-to-impact; our EDR missed it; we tuned the rule; we retested; now it blocks and alerts in under 10 minutes.” At Filigran, we call it Continuous Threat-Led Exposure Management (CTEM).

Conclusion
CTEM approach is only valuable if it moves you from noise to outcomes. The goal isn’t to adopt a new acronym or buy another platform; it’s to continuously answer, with evidence, the questions that matter: what can actually hurt us, how would it happen, and are we able to stop it? That requires more than expanded scanning or prettier dashboards. CTEM, done right, is not something a vendor “delivers” but a way your organization chooses to run security: threat‑led, context‑aware, and relentlessly validated.
Filigran’s OpenCTI and OpenAEV are designed to enable this reality. OpenCTI brings structured, relevant threat context into your environment; OpenAEV turns that context into continuous, adversary‑aligned validation and mobilization. Together, they help you close the loop from ‘we know about this threat’ to ‘we have proven we can detect, block, and respond to it’ – not once, but continuously.
That is the real promise of CTEM: less guesswork, fewer vanity metrics, and a security program grounded in evidence, aligned to business risk, and capable of adapting as fast as your adversaries.
If you’d like to discuss more about this topic, don’t hesitate to start a conversation on Filigran Community or get in touch with us!
Read more
Explore related topics and insights






