BAS to AEV and a Move Towards Unified Exposure Management
Security validation is experiencing its most exciting transformation in years, as organizations embrace a more strategic and proactive approach to understanding their true security posture. With numerous diverse tools in any typical security stack, its only reasonable that due focus is given to validate the effectiveness of these tools. This transformation is driven by two game-changing capabilities that CISOs and security leaders have long sought and is now coming together: unified exposure management that provides visibility and context across complex hybrid infrastructures, and continuous security validation that delivers real-time confidence in defensive capabilities.
This transformation is shaping up a new solution space – Adversarial Exposure Validation (AEV). Read on if you would like to:
- Understand the convergence towards exposure management and role AEV plays in it
- Know what to look out for in an AEV solution
- Go beyond security tools validation, test your human readiness also
Turning Exposure into Action
Amid expanding attack surfaces and a surge of vulnerabilities, organizations are looking for clear visibility into which exposures are truly exploitable. Vulnerability management alone is no longer sufficient and we need to go beyond CVEs to risk-based exposure management – to identify most probable threats, attack paths, and exploitable configurations. A proactive approach to find, prioritize, and eliminate the conditions that let attacks succeed, based on an individual organization exposures.
A unified and continuous exposure management approach empowers CISOs to address these areas:
- Cutting through the noise: What are the truly exploitable vulnerabilities and most probably attack paths that we need to emulate in our environment?
- Reality check: Are our security investments actually stopping attacks, or are we flying blind with tools that look good on dashboards but fail when tested?
- The 3 AM test: When crisis hits, will my team respond with confidence built from practice, or chaos from inexperience?
According to Gartner, organizations can reduce frequency and impact of cyberattacks by 50%, by enriching SOC data with exposure information.
Rise of Adversarial Exposure Validation: BAS 2.0?
Adversarial Exposure Validation (AEV) is emerging as a crucial component of exposure management, to create a context-aware validation ecosystem that finally answers the question: what can actually hurt us and how do we stop it?
Gartner defines AEV as ‘technologies that deliver consistent, continuous, and automated evidence of the feasibility of an attack.’ Its about proactively assessing adversary’s TTPs and most probable attack paths in a continuous loop. Emphasis here is on continuous validation and security optimization and in that sense it goes beyond traditional Breach and Attack Simulation (BAS). We don’t see AEV as a replacement of BAS rather as evolution of BAS itself. With an AEV platform, you can:
- Validate your defenses by emulating attacker behavior;
- Continuously find and prioritizes the conditions that would let an attacker succeed;
- And finally, get remediation guidance to fix the gaps.
In short, BAS to AEV evolution is from ‘can we detect it?’ to ‘let’s eliminate it.’
| BAS | AEV | |
|---|---|---|
| Primary Goal | Technical validation | Reduce business risk by Improving security posture |
| Cadence | Scheduled testing of specific scenarios | Continuous testing, validation and remediation |
| Focus Area | Primarily focused on TTPs and attack simulations | More realistic and customizable scenarios using a combined approach of simulations and emulations to validate all three – security tools, processes and people |
| Evolution path | Converging towards AEV – with capabilities combining breach simulation, automated workflows and AI-powered scaling of operations e | Integration with broader exposure management programs and a move towards Continuous Threat Exposure Management (CTEM) |
What to look out for in an AEV Solution?
AEV is an evolving space and has relevance for various security teams including SOC/blue team, pentesting/threat hunting/red team and purple team. Its usage depends on your initial use case and scope based on your critical assets, business process and incident response plan. However, at the bare minimum, an AEV tool should provide you the following options:
- Wide coverage: ability to emulate a wide variety of attacks across the entire cyber kill chain by using industry standard frameworks like MITRE ATT&CK, NIST, Caldera etc
- Prioritization: capability to prioritize threats and vulnerabilities to map the most probable attack paths
- Flexible scenarios: customizable scenarios and payloads, pre-packaged scenarios library
- Automated workflows: no-code AI-assisted scenario creation and automated workflows to scale your red team capability and ease of use for non-technical use cases like tabletop exercises
- Recurring scenarios to show posture improve overtime and to be able to track Mean Time to Remediation (MTTR)
- Remediation guidance: assess how well your detection rules are working and remediation guidance on vulnerability patching with multiple options
How are we evolving our AEV capabilities?
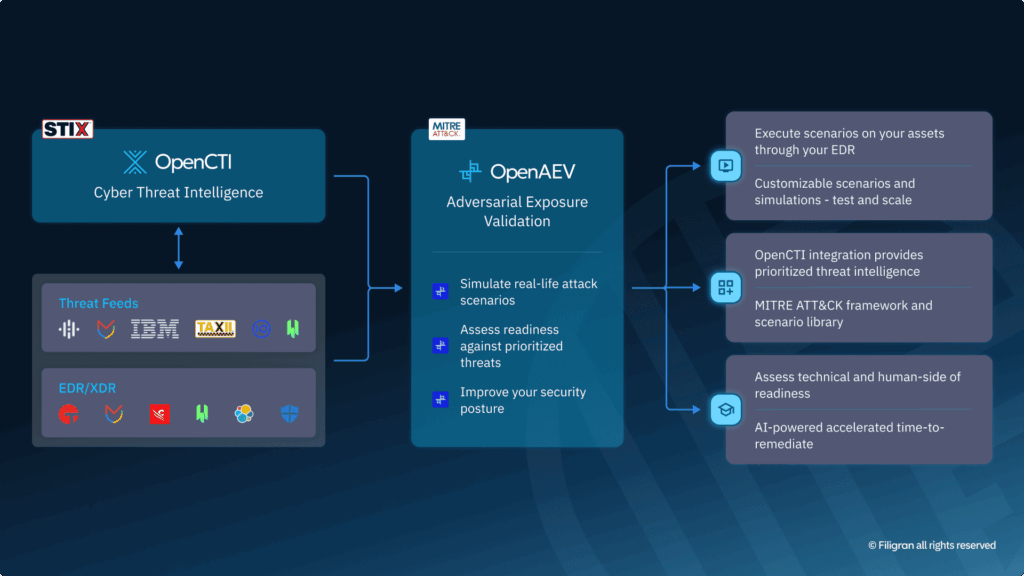
Since Filigran’s inception in 2022, our eXtended Threat Management (XTM) suite has been evolving with a clear vision towards threat-informed defense. In this context, our product strategy has already been industry leading. Our first offering as part of the XTM suite was OpenCTI, to operationalize threat intelligence with end-to-end threat lifecycle management capabilities. Then came OpenBAS Community Edition (CE) with simulation and security validation capabilities, which made OpenCTI’s intel output truly actionable. And now we have added enterprise grade features to it including automated workflows, AI-assisted scenario creation & remediation guidance, ability to run simulations with customer specific EDR agents. To acknowledge this evolution from pure control validation to full adversarial exposure management, its only appropriate that we refer to our new (still open-source) AEV platform as OpenAEV.
While OpenCTI provides threat and exposure assessment capabilities, OpenAEV makes it directly actionable to validate and improve security posture. Benefitting from bi-directional integration between OpenCTI and OpenAEV, customers can build scenarios based on prioritized threat intelligence from within OpenCTI itself, and execute them directly in OpenAEV.
The continuous exposure discovery, attack‑path mapping, prioritization, and remediation guidance provides some of the broadest exposure management capabilities available on the market today.
OpenAEV as AEV+
With OpenAEV, you can optimize not just your security stack, but your security processes and incident response plans too. Traditional tabletop or crisis management exercises are run like fire drills – necessary, but hardly sufficient.
The challenge has always been scale. But with OpenAEV, you standardize, automate and scale tabletop exercises. By integrating human readiness testing into our OpenAEV platform, we’re also addressing CTEM’s mobilization challenge at scale. Every validation cycle becomes an opportunity to test not just if you can detect a threat, but whether your team can effectively respond to it. Can they mobilize the right resources? Make the right decisions? Communicate effectively with stakeholders?

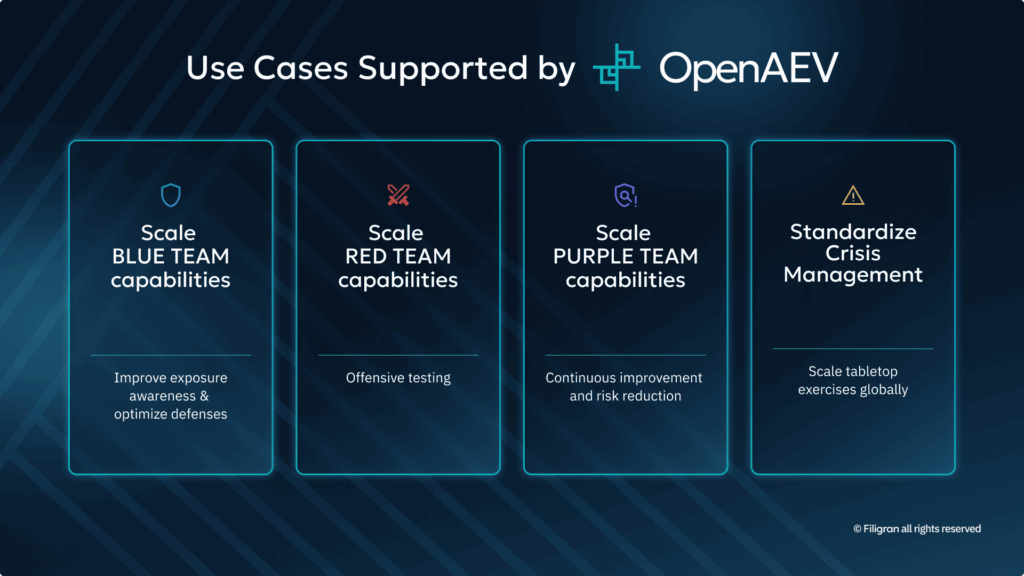
Use Cases Supported by OpenAEV
- Scale blue team capabilities
- Improve exposure awareness: leverage OpenCTI to automatically build scenarios by utilizing Prioritized Threat Intelligence (PIR)
- Optimize defenses: Validate security platform with realistic scenrios and improve security posture through guided remediation
2. Scale red team capabilities
- Offensive testing: Run deep simulations to understand particular threat actors’ or campaigns’ attack paths and movements
3. Scale purple team capabilities
- Continuous improvement and risk reduction: Centralize purple team’s exercises with both red & blue team to implement a continuous posture improvement plan with timelines.
4. Standardize crisis management:
- Globally scale tabletop exercises with a dynamic, ease-to-use platform instead of doing manual preparations and using Excel files.
Conclusion
The progression from BAS to AEV to human-integrated validation represents the maturation of security testing. We’re finally acknowledging what we’ve always known: security is as much about people as it is about technology.
AEV platforms that incorporate human readiness testing aren’t just evolving beyond BAS, they’re completing the CTEM cycle. They’re not just finding and validating exposures; they’re ensuring your team can effectively mobilize when those exposures are exploited.
If you’d like to learn more about OpenAEV, our open-source XTM suite or how we can help with exposure management or CTEM intitiatives, visit our website or contact us to speak directly with our team.
Feel free to participate and contribute to the broader security community’s knowledge by joining our Slack community today.
Read more
Explore related topics and insights






